smart card power consumption Power analysis is a type of side-channel attack, where the instantaneous power consumption of a device can be used to compromise the secret it holds. This is possible since the consumption of a device depends on the data and operations that are being processed.
Go to the "Settings" app on your iPhone. Scroll down and tap on "Wallet & Apple Pay." On the "Wallet & Apple Pay" screen, you'll see an option to turn on "NFC Scanning or NFC tag reader." Toggle this switch to the "On" .
0 · Power Analysis for Smartcard's Authentication
1 · Examining smart
Marc Auburn. Un expérienceur pragmatique; Introduction du livre 0,001%; Interviews de Marc Auburn; Vidéos de Marc Auburn; Stages – Meetings – rencontres. Tester nos lampes Hypnagogiques; . Liens vers les podcasts: .
Power Analysis for Smartcard's Authentication
This paper examines how monitoring power consumption signals might breach smart-card security. Both simple power analysis and differential power analysis attack.
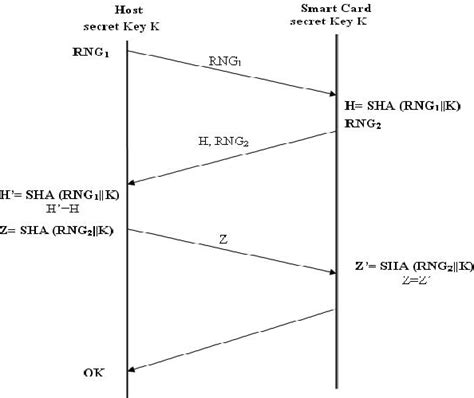
In this paper, we present an authentication protocol implementation dedicated for smart cards and we analyze the power consumption of contact and contactless ones by the Simple Power .
This paper examines how monitoring power consumption signals might breach smart-card security. Both simple power analysis and differential power analysis attack.In this paper, we present an authentication protocol implementation dedicated for smart cards and we analyze the power consumption of contact and contactless ones by the Simple Power Analyze (SPA) techniques.
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video record.Power analysis is a type of side-channel attack, where the instantaneous power consumption of a device can be used to compromise the secret it holds. This is possible since the consumption of a device depends on the data and operations that are being processed. The attack reveals the secret key of AES software implementations on smart cards by exploiting the fact that the power consumption of most smart-card processors leaks information during the AES key expansion.A major breakthrough in side channel attacks came up when analysis of power consumption by a cryptographic device led to discovery of the secret key. This analysis technique popularly known as Power Analysis Attack is now one of the most volatile and successful side channel attacks.
Examining smart
In this article we describe an efficient AES software imple-mentation that is well suited for 8-bit smart cards and resistant against power analysis attacks. Our implementation masks the intermediate sults and randomizes the sequence of operations at the beginning and end of the AES execution. This is measured the power consumption of the smart card with an oscilloscope. The acquired information can be analysed to determine information on what is occurring within a secure microprocessor.Well-equipped electronics labs have equipment that can digitally sample voltage differences at extraordinarily high rates (over 1GHz) with excellent ac-curacy.[1] A figure showing the traces of a smart card’s power consumption is illustrated below. Figure .
This paper examines how monitoring power consumption signals might breach smart-card security, and develops an approach to model the signal-to-noise ratio (SNR) and shows how this SNR can be significantly improved using a multiple-bit attack.This paper examines how monitoring power consumption signals might breach smart-card security. Both simple power analysis and differential power analysis attack.In this paper, we present an authentication protocol implementation dedicated for smart cards and we analyze the power consumption of contact and contactless ones by the Simple Power Analyze (SPA) techniques.
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video record.
Power analysis is a type of side-channel attack, where the instantaneous power consumption of a device can be used to compromise the secret it holds. This is possible since the consumption of a device depends on the data and operations that are being processed. The attack reveals the secret key of AES software implementations on smart cards by exploiting the fact that the power consumption of most smart-card processors leaks information during the AES key expansion.A major breakthrough in side channel attacks came up when analysis of power consumption by a cryptographic device led to discovery of the secret key. This analysis technique popularly known as Power Analysis Attack is now one of the most volatile and successful side channel attacks.
In this article we describe an efficient AES software imple-mentation that is well suited for 8-bit smart cards and resistant against power analysis attacks. Our implementation masks the intermediate sults and randomizes the sequence of operations at the beginning and end of the AES execution. This is measured the power consumption of the smart card with an oscilloscope. The acquired information can be analysed to determine information on what is occurring within a secure microprocessor.
Well-equipped electronics labs have equipment that can digitally sample voltage differences at extraordinarily high rates (over 1GHz) with excellent ac-curacy.[1] A figure showing the traces of a smart card’s power consumption is illustrated below. Figure .
lettore smart card mediaworld
Using NFC on Your IPhone. Hold the NFC tag near your iPhone to read it automatically. If you have an older iPhone, open the Control Center and tap the NFC icon. Move the tag over your phone to activate it. The NFC can .Feb 20, 2023 12:40 AM in response to samarat00. NFC, Near-field communication - Apple Developer. Near-field communication (NFC) enables devices within a few centimeters of each other to exchange information wirelessly. iOS apps running on supported. iOS 16.3, Cant find .
smart card power consumption|Examining smart