rfid chip will explode upon taking it out If tags are placed on products that bang into one another during shipping, the chip in the transponder could become crushed, rendering the tag inoperable. If a tag is placed on a . $17.95
0 · rfid chip breakdown
1 · removing rfid chip credit card
2 · can rfid tag break down
Here is how the “Handheld RFID Writer” (that you can easily purchase for less than $10) works: Turn on the device. Hold a compatible EM4100 card or fob to the side facing the hand grip and click the ‘Read’ button. The .
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!If tags are placed on products that bang into one another during shipping, the chip in the transponder could become crushed, rendering the tag inoperable. If a tag is placed on a .
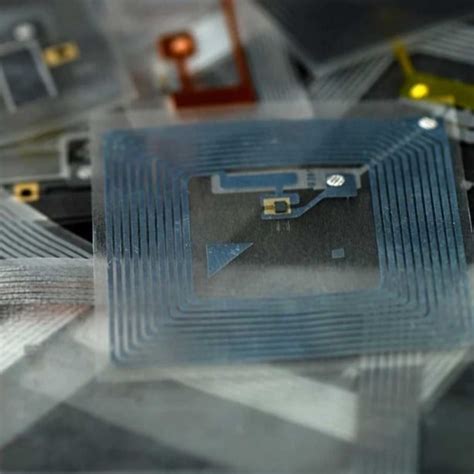
small nfc tags
If you're concerned that a credit card's RFID chip is putting your personal data at risk, why not just drill the darn thing out? Not so fast, says Joel Dubin. In this . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!If tags are placed on products that bang into one another during shipping, the chip in the transponder could become crushed, rendering the tag inoperable. If a tag is placed on a .
Security Risks. RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal .
samsung galaxy s4 mini nfc tags
If you're concerned that a credit card's RFID chip is putting your personal data at risk, why not just drill the darn thing out? Not so fast, says Joel Dubin. In this . If an RFID chip presence is confirmed, individuals have options available to them, including seeking professional removal, documenting evidence, reporting the incident, . Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; . An x-ray showing a Walletmor RFID chip injected into a person’s hand after a local anesthetic. The company’s literature on its website says: “Forget about the cash, card, and .
programming an nfc tag windows 10
In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process .
RFID cards are very simple devices, which makes them reliable for everyday use. However, it also makes them an easy target for attackers looking to gain access to a facility. In .Wireless identity theft, also known as contactless identity theft or RFID identity theft, is a form of identity theft described as "the act of compromising an individual’s personal identifying . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!If tags are placed on products that bang into one another during shipping, the chip in the transponder could become crushed, rendering the tag inoperable. If a tag is placed on a .
Security Risks. RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal .
If you're concerned that a credit card's RFID chip is putting your personal data at risk, why not just drill the darn thing out? Not so fast, says Joel Dubin. In this .
If an RFID chip presence is confirmed, individuals have options available to them, including seeking professional removal, documenting evidence, reporting the incident, . Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; .
rfid chip breakdown
removing rfid chip credit card
An x-ray showing a Walletmor RFID chip injected into a person’s hand after a local anesthetic. The company’s literature on its website says: “Forget about the cash, card, and . In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process .
RFID cards are very simple devices, which makes them reliable for everyday use. However, it also makes them an easy target for attackers looking to gain access to a facility. In .
can rfid tag break down

rfid tag nfc
securitas vision nfc tag
For merchants, this translates to fewer contested transactions, lower operational costs associated with managing disputes, and improved overall financial stability. Card-present payments have lower chargeback rates and .
rfid chip will explode upon taking it out|removing rfid chip credit card