authentication with smart cards radius The purpose of this document is to demonstrate how ISE authenticate / authorize a user tha. Time, TV schedule. TV Channel: SEC Network. Start time: 11:45 a.m. CT. Auburn vs. ULM will be broadcast nationally on SEC Network in Week 12 of the college football season. .Statewide coverage is the hallmark of the Auburn Sports Network's exclusive coverage of Auburn football. All home and away games are broadcast across the entire state .
0 · radius server ca certificate
1 · radius server authentication
2 · radius authentication sqlnet
3 · radius authentication protocol
4 · oracle radius authentication
Only the Loftwing amiibo drops "just" random foodstuff as it doesn't register as a Zelda-themed amiibo in BotW and thus behaves like a generic, random one. . Considering the cost of an .
The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. This document describes the components used for this setup, configuration.
The purpose of this document is to demonstrate how ISE authenticate / authorize a user tha.The Cisco Community is an engaging, full-featured, self-service, content-filled, technical com. The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. This document describes the components used for this setup, configuration.This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .
Interactive sign-in in Windows begins when the user presses CTRL+ALT+DEL. The CTRL+ALT+DEL key combination is called a secure attention sequence (SAS). To keep other programs and processes from using it, Winlogon registers this sequence during the boot process.
radius server ca certificate
radius server authentication
An Oracle Database network can use any authentication method that supports the RADIUS standard. The supported RADIUS standard includes token cards and smart cards when you install and configure the RADIUS protocol. Oracle Database uses . The goal for the intended environment is to allow users to connect to the wireless network via their AD user credentials, but if the machine or device they are using is NOT a domain joined device, deny them access to internal resources (such as sensitive files in file shares not meant to spill onto unapproved devices) You can use smart card authentication to streamline the logon process for your users while also enhancing the security of user access to your infrastructure. Access to the internal corporate network is protected by certificate-based two-factor authentication using the public key infrastructure.Some on-premises applications use RADIUS authentication and require MFA controls. Some on-premises applications require physical smart cards to authenticate. Transition to Phishing-Resistant Authentication.
Introduction. This document describes how to configure Client Certificate-based authentication for Identity Services Engine (ISE) management access. In this example, the ISE administrator authenticates against the User certificate to gain Admin accessto the Cisco Identity Services Engine (ISE) management GUI. Prerequisites. Requirements.Turnkey network security environments in which applications support the RADIUS protocol, such as in an access environment that uses a smart card access control system. In one case, RADIUS has been used with Enigma’s security cards to validates .Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.
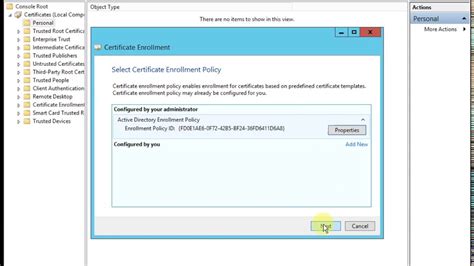
The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. This document describes the components used for this setup, configuration.This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .
radius authentication sqlnet
Interactive sign-in in Windows begins when the user presses CTRL+ALT+DEL. The CTRL+ALT+DEL key combination is called a secure attention sequence (SAS). To keep other programs and processes from using it, Winlogon registers this sequence during the boot process.An Oracle Database network can use any authentication method that supports the RADIUS standard. The supported RADIUS standard includes token cards and smart cards when you install and configure the RADIUS protocol. Oracle Database uses .
The goal for the intended environment is to allow users to connect to the wireless network via their AD user credentials, but if the machine or device they are using is NOT a domain joined device, deny them access to internal resources (such as sensitive files in file shares not meant to spill onto unapproved devices) You can use smart card authentication to streamline the logon process for your users while also enhancing the security of user access to your infrastructure. Access to the internal corporate network is protected by certificate-based two-factor authentication using the public key infrastructure.Some on-premises applications use RADIUS authentication and require MFA controls. Some on-premises applications require physical smart cards to authenticate. Transition to Phishing-Resistant Authentication.Introduction. This document describes how to configure Client Certificate-based authentication for Identity Services Engine (ISE) management access. In this example, the ISE administrator authenticates against the User certificate to gain Admin accessto the Cisco Identity Services Engine (ISE) management GUI. Prerequisites. Requirements.
gemalto smart card utilities
Turnkey network security environments in which applications support the RADIUS protocol, such as in an access environment that uses a smart card access control system. In one case, RADIUS has been used with Enigma’s security cards to validates .

radius authentication protocol
Auburn football radio station 2024 Radio station: WGZZ 94.3 FM, SiriusXM Fans can catch every game of the 2024 Auburn football season on WGZZ 94.3 FM, the Tigers' .
authentication with smart cards radius|oracle radius authentication